This page was exported from All The Latest MCTS Exam Questions And Answers For Free Share
[
https://www.mctsdump.com
]
Export date: Wed May 8 1:00:40 2024 / +0000 GMT
[Free-Dumps] 100 Percent Pass 400-251 By Learning PassLeader Free 400-251 Study Guide (Question 271 – Question 300)
New Updated 400-251 Exam Questions from PassLeader 400-251 PDF dumps! Welcome to download the newest PassLeader 400-251 VCE dumps: http://www.passleader.com/400-251.html (366 Q&As) Keywords: 400-251 exam dumps, 400-251 exam questions, 400-251 VCE dumps, 400-251 PDF dumps, 400-251 practice tests, 400-251 study guide, 400-251 braindumps, CCIE Security Exam p.s. Free 400-251 dumps download from Google Drive: https://drive.google.com/open?id=0B-ob6L_QjGLpd3JLalNVS0VWbms QUESTION 271 A. Network translation mode Answer: B QUESTION 272 A. SCEP Answer: A QUESTION 273 A. Category: internet Answer: A QUESTION 274 Answer: D QUESTION 275 A. It can apply security policies on an individual user or user-group basis Answer: AD QUESTION 276 A. The current public key of the router is deleted from the cache when the router reboots, and the router generates a new one. Answer: C QUESTION 277 A. The device will close each connection after 90 seconds even if a connection is actively processing a request. Answer: CE QUESTION 278 A. They support an implicit deny Answer: AB QUESTION 279 A. Require users to authenticate before accessing the network Answer: BC QUESTION 280 A. The binding database stores information about trusted interface. Answer: CD QUESTION 281 A. Inadvertent packet loss can occur when loose mode is used with asymmetrical routing. Answer: DEF QUESTION 282 A. TTL Answer: CDF QUESTION 283 A. IP msdpsa-filter in <peer>[list<acl>] [route-map <map> ] Answer: B QUESTION 284 A. The AES algorithm is an asymmetric block cipher. Answer: BE QUESTION 285 A. CoPP Answer: E QUESTION 286 A. Teredo tunnelling Answer: E QUESTION 287 Answer: QUESTION 288 A. PQ Answer: D QUESTION 289 A. Its enables the NHRP FIB lookup process to perform route summarization on the hub. Answer: BE QUESTION 290 A. The DES algorithm is based on asymmetric cryptography. Answer: CE QUESTION 291 A. Aggressive Answer: CF QUESTION 292 A. Established Answer: CE QUESTION 293 A. SNAT Answer: DF QUESTION 294 A. The finger service Answer: C QUESTION 295 Answer: QUESTION 296 A. On the connecting leaf switches Answer: A QUESTION 297 A. Traffic shaping and standard priority queuing on the same interface. Answer: CDF QUESTION 298 A. CAR Answer: B QUESTION 299 A. It allows the ASA to function as a multicast router. Answer: DE QUESTION 300 A. It includes a congestion control mechanism Answer: AE Download the newest PassLeader 400-251 dumps from passleader.com now! 100% Pass Guarantee! 400-251 PDF dumps & 400-251 VCE dumps: http://www.passleader.com/400-251.html (366 Q&As) (New Questions Are 100% Available and Wrong Answers Have Been Corrected! Free VCE simulator!) p.s. Free 400-251 dumps download from Google Drive: https://drive.google.com/open?id=0B-ob6L_QjGLpd3JLalNVS0VWbms
Which Cisco ASA firewall mode supports ASDM one-time-password authentication using RSA SecurID?
B. Single-context routed mode
C. Multiple-context mode
D. Transparent mode
What protocol is responsible for issuing certificates?
B. DTLS
C. ESP
D. AH
E. GET
Which category to protocol mapping for NBAR is correct?
Protocol: FTP, HTTP, TFTP
B. Category: Network management
Protocol: ICMP, SNMP, SSH, telent
C. Category: network mail services
Protocol: mapi, pop3, smtp
D. Category: Enterprise applications
Protocal: citrixICA, PCAnywhere, SAP, IMAP
You have discovered unwanted device with MAC address 001c.0f12.badd on port FastEthernet1/1 on VLAN 4. What command or command sequence can you enter on the switch to prevent the MAC address from passing traffic on VLAN 4?
Which two options are benefits of the Cisco ASA Identity Firewall? (Choose two.)
B. It can identify threats quickly based on their URLs
C. It can operate completely independently of other services
D. It decouples security policies from the network topology
E. It supports an AD server module to verify identity data
Refer to the exhibit. Which effect of this command is true?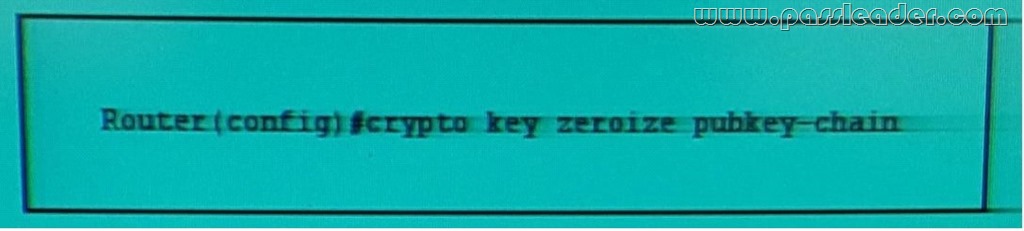
B. The CA revokes the public key certificate of the router.
C. The public key of the remote peer is deleted from the router cache.
D. The router immediately deletes its current public key from the cache and generates a new one.
E. The router sends a request to the CA to delete the router certificate from its configuration.
Refer to the exhibit. If you apply the given command to a Cisco device running IOS or IOS XE, which two statements about connections to the HTTP server on the device are true? (Choose two.)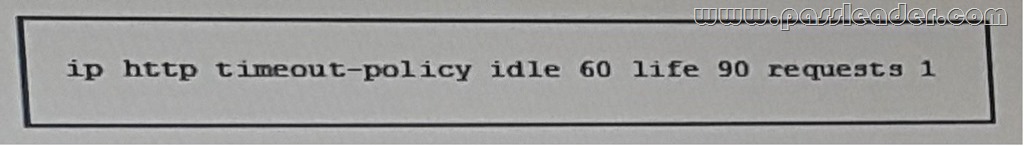
B. Connections will close after 60 seconds without activity or 90 seconds with activity.
C. Connections will close after 60 seconds or as soon as the first request is processed.
D. When you apply the command , the device will immediately close any existing connections that have been open for longer than 90 seconds.
E. Connections will close after 60 seconds without activity or as soon as the first request is processed.
Which two statements about global ACLs are true? (Choose two.)
B. They are applied globally instead of being replicated on each interface
C. They override individual interface access rules
D. They require an explicit deny
E. They can filer different packet types than extended ACLs
F. They require class-map configuration
What are two security controls you can implement to protect your organization's network from virus and worm outbreak? (Choose two.)
B. Quarantine hosts that fail to meet your organization's IT security requirements
C. Implement Cisco Identity Service Engine (ISE) for network security
D. Implement routing protocols with strong interface authentication
E. Deploy Cisco prime LMS to manage network security
Which two statement about DHCP snooping are true? (Choose two.)
B. Massages sent from outside the service-provider network are untrusted.
C. The binding database stores information about both IP and MAC addresses.
D. The lease time in the binding database is a pre-set value.
E. DHCP servers connect to untrusted interface on the switch.
Which three statements about Unicast RPF in strict mode and loose mode are true? (Choose three.)
B. Strict mode requires a default route to be associated with the uplink network interface.
C. Both loose and strict modes are configured globally on the router.
D. Loose mode requires the source address to be present in the routing table.
E. Strict mode is recommended on interfaces that will receive packets only form the same subnet to which the interface is assigned.
F. Interfaces in strict mode drop traffic with return routes that point to the NULL 0 interface.
What are three IPv6 extension headers? (Choose three.)
B. source option
C. Destination options
D. Authentication
E. Segment
F. Hop-by-Hop options
What command specifies the peer from which MSDP SA message are accepted?
B. Ipmsdp default-peer <peer>
C. Ipmsdp mesh-group
D. Ipmsdp originator-id <interface>
Which two statements about the AES algorithm are true? (Choose two.)
B. The AES algorithm operates on a 128-bits block.
C. The AES algorithm uses a fixed length-key of 128 bits.
D. The AES algorithm does not give any advantage over 3DES due to the same key length.
E. The AES algorithm consist of four functions. Three functions provide confusion-diffusion and one provides encryption.
Which feature can prevent IP spoofing attacks?
B. CBAC
C. ARP spoofing
D. TCP Intercept
E. Unicast RPF
F. CAR
What technique can an attacker use to obfuscate a malware application payload, allowing it to bypass standard security mechanisms?
B. Decryption
C. A PE32 header
D. Steganography
E. BASE64
Drag and Drop Question
Drag each EAP variant in the 802.1X framework on the left to the matching statement on the right.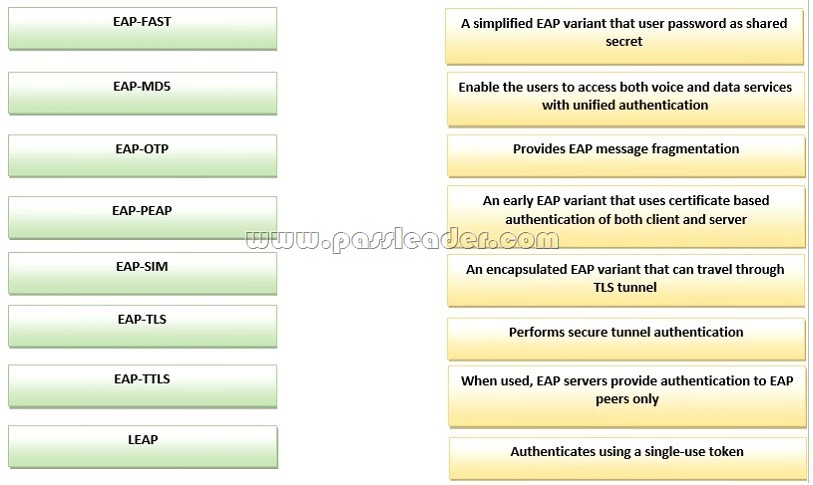

Refer to the exhibit. What feature must be implemented on the network to produce the given output?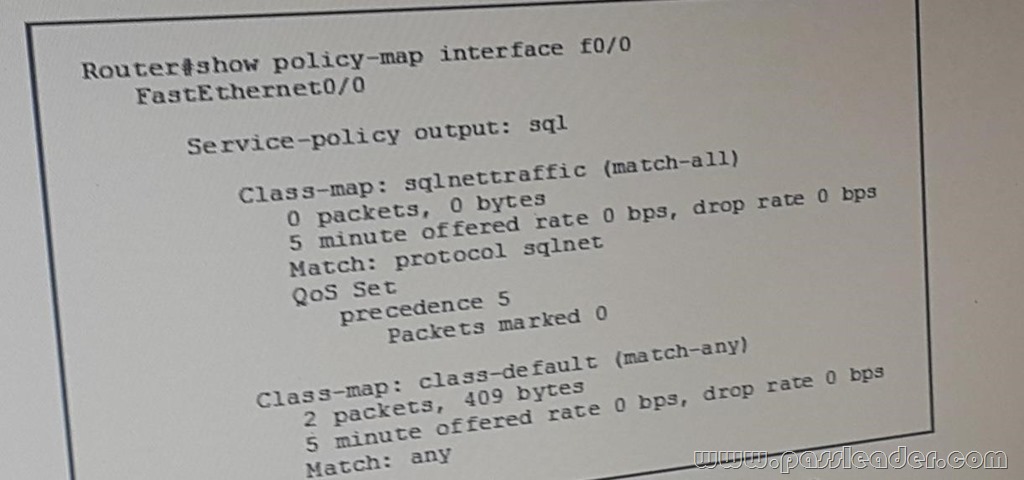
B. CQ
C. WFQ
D. NBAR
E. CAR
Which two options are benefits of shortcut Switching Enhancements for NHRP on DMVPN networks? (Choose two.)
B. It allows data packets to be fast switched while spoke-to-spoke tunnels are being established.
C. It is most beneficial with partial full-mesh DVMPN setup.
D. It supports layered network topologies with the central hubs and direct spoke-to-spoke tunnels between spokes on different hubs.
E. It enables spokes to use a summary route to build spoke-to-spoke tunnels.
Which two statements about the DES algorithm are true? (Choose two.)
B. The DES algorithm is a stream cipher.
C. The DES algorithm is based on symmetric cryptography.
D. The DES algorithm encrypts a block of 128 bits.
E. The DES algorithm uses a 56-bit key.
What are the two IPSec modes? (Choose two.)
B. ISAKMP
C. Transport
D. IKE
E. Main
F. Tunnel
Which two options are unicast address types for IPv6 addressing? (Choose two.)
B. Static
C. Global
D. Dynamic
E. Link-local
What are the two technologies that support AFT? (Choose two.)
B. NAT -6to4
C. DNAT
D. NAT -PT
E. NAT -PMP
F. NAT64
Refer to the Exhibit. Which service or feature must be enabled on 209.165.200.255 produce the given output?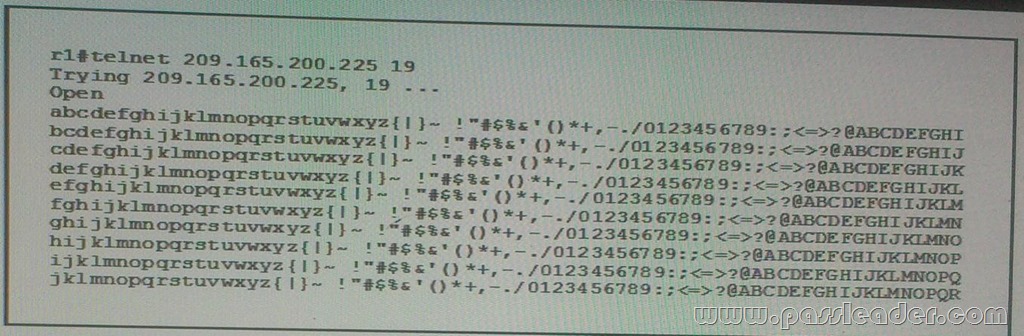
B. A BOOTp server
C. A TCP small server
D. The PAD service
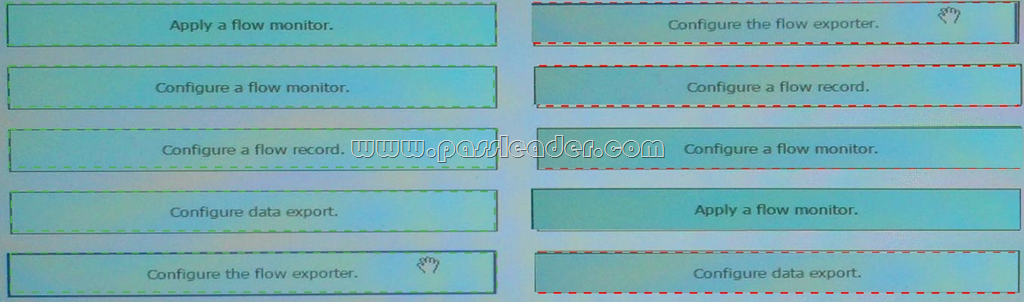
Drag and Drop Question
Drag each step in the configuration of flexiblenetflow IPv6 traffic Unicast flows on the left into the Correct order of operation on the right.
You want to allow existing network hardware (which is not part of the ACI infrastructure) to be governed by the APIC, by installing device packages. Where must these packages be installed?
B. On the APIC
C. On the network element you are adding
D. On all devices on the path
What are three QoS features supported on the ASA running version 8.x? (Choose three.)
B. IPSec-over-TCP priority queuing.
C. Traffic shaping within the class-default class map only.
D. Priority queuing.
E. Traffic shaping within any class map.
F. Traffic policing.
What IOS feature can prevent header attacks by using packet-header information to classify traffic?
B. FPM
C. TOS
D. LLQ
E. TTL
Which two statement about MLD version 2 on the ASA are true? (Choose two.)
B. It enables the ASA to discover multicast address listeners on attached and remote links.
C. It discover other multicast address listeners by listening to multicast listener reports.
D. It enables the ASA to discover multicast address listeners to attached links only.
E. It sends multicast listener reports in response to multicast listener quires.
Which two characteristics of DTLS are true? (Choose two.)
B. It supports long data transfers and connections data transfers
C. It completes key negotiation and bulk data transfer over a single channel
D. It is used mostly by applications that use application layer object-security protocols
E. It includes a retransmission method because it uses an unreliable datagram transport
F. It cannot be used if NAT exists along the path
Post date: 2017-02-14 10:38:07
Post date GMT: 2017-02-14 10:38:07
Post modified date: 2017-02-14 10:38:07
Post modified date GMT: 2017-02-14 10:38:07
Powered by [ Universal Post Manager ] plugin. MS Word saving format developed by gVectors Team www.gVectors.com