Get New Valid 70-680 Exam Dumps To Pass Exam Easily: The following new 70-680 exam questions were updated in recent days by PassLeader, visit passleader.com to get the full version of new 580q 70-680 exam dumps with free version of new VCE Player software, our valid 70-680 briandumps will help you passing 70-680 exam easily! 70-680 PDF practice test and VCE are all available now!
keywords: 70-680 exam,580q 70-680 exam dumps,580q 70-680 exam questions,70-680 pdf dumps,70-680 vce dumps,70-680 braindumps,70-680 practice test,70-680 study guide,TS: Windows 7, Configuring Exam

QUESTION 341
You have a computer that runs Windows 7 and Windows Internet Explorer 8. You have a third-party Internet Explorer toolbar installed on the computer. You need to temporarily disable the toolbar. The solution must not affect any other installed toolbars. What should you do?
A. Start an Inprivate Browsing session.
B. Run Msconfig.exe and enable Selective Startup.
C. From the Tools menu, select Compatibility View Settings.
D. From the Tools menu, open Manage Add-ons and modify the add-on settings.
Answer: D
Explanation:
Add-Ons and Search Providers. Add-ons extend the functionality of Internet Explorer. Add-ons are usually downloaded and installed separately rather than being included with Internet Explorer. You manage add-ons through the Manage Add-Ons dialog box. Toolbars and Extensions This area lists browser toolbars and extensions. Toolbars are additions to browsersthat add extra functionality to the browser interface. Extensions allow the browser to perform additional functions, such as playing media or opening some types of document file within the browser that the browser does not support natively.
QUESTION 342
You have two computers named Computer1 and Computer2 that run Windows 7. You use Remote Desktop to connect from Computer1 to Computer2. You need to prevent the desktop background of Computer2 from being displayed when you use Remote Desktop to connect to Computer2. What should you do on Computer1?
A. From the Personalization options, change the theme.
B. From the System properties, modify the Remote settings.
C. From the Remote Desktop Connection options, modify the Performance setting.
D. From the Remote Desktop Connection options, modify the Display configuration settings.
Answer: C
Explanation:
Configuring the Desktop ExperienceYou can configure the connection speed and fine-tune the desktop environment for optimal performance by using the settings located on the Experience tab of the Remote Desktop Connection tool. Most of these settings relate to the graphical nature of the desktop. Because the processing for graphics happens on the server and must be transmitted to the desktop over the network connection, you can increase performance by allowing only the minimal settings that are necessary for your users. When you choose a connection speed, the check boxes are automatically selected to indicate the recommended settings for the richest visual experience possible at that speed.ExperienceConfigure the connection speed and adjust the desktop environment for optimal performance.Desktop background Allows user to choose a custom background or wallpaper for their desktop. Because these can be very graphicintensive, disable this setting unless it is necessary for your users.
QUESTION 343
You have a computer that runs Windows 7. You add a new hard disk drive to the computer and create a new NTFS partition. You need to ensure that you can use the Previous Versions feature on the new drive. What should you do?
A. From Disk Management, convert the new disk to a dynamic disk.
B. From System Properties, configure the System Protection settings.
C. From System and Security, enable BitLocker Drive Encryption (BitLocker).
D. From the properties of the new drive, create a share and modify the caching settings.
Answer: B
Explanation:
System protection might not be turned on for the drive. If system protection is not turned on, Windows can’t create previous versions.To turn on system protection:
1. Click to open System.
2. In the left pane, click System protection. If you’re prompted for an administrator password or confirmation, type the password or provide confirmation.
3. Click the drive, and then click Configure.
4. Click Restore system settings and previous versions of files, and then click OK.
QUESTION 344
You have a computer that contains the folders shows in the following table:
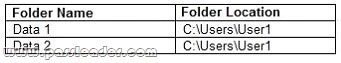
You accidentally delete the Data1 folder. You need to restore the contents of the Data1 folder. The solution must not overwrite any changes to the Data2 folder. What should you do?
A. From Recovery, restore a system restore point.
B. From the Previous Versions tab of the User1 folder, click Copy.
C. From the Sharing tab of the User1 folder, modify the Caching settings.
D. Start the computer and then press F8. Restore the Last Known Good Configuration.
Answer: B
QUESTION 345
You have a computer that runs Windows XP Service Pack 3 (SP3). The computer is a member of an Active Directory domain. Several domain users log on to the computer. You plan to install Windows 7 on the computer. You need to ensure that all user settings are preserved after the installation. What should you do?
A. Run Loadstate.exe, install Windows 7, and then run Scanstate.exe.
B. Run Sysprep.exe /audit, install Windows 7, and then run Sysprep.exe /oobe.
C. Run Windows Easy Transfer, install Windows 7, and then run Windows Easy Transfer again.
D. Create a backup of %systemdrive%\documents and settings, install Windows 7, and then restore the backup.
Answer: C
Explanation:
Windows Easy Transfer. Windows Easy Transfer is a utility that comes with Windows 7 that you can use to transfer user profile data from computers running Windows XP, Windows Vista, or Windows 7 to new computers running Windows 7. Windows Easy Transfer can be used to transfer user accounts, documents, music, pictures, e-mail, bookmarks, certificates, and other data. External Hard Disk or USB Flash Drive You can specify an attached external hard disk or USB flash drive. It is also possible to specify an internal hard disk drive or network share when using this method. You can perform a side-by-side migration as well as a wipe-and- restore migration using this method. You protect your data by entering a password on the source computer that you must again enter before importing the data on the destination computer.
QUESTION 346
You have two computers named Computer1 and Computer2. Computer1 runs Windows Vista. Computer2 runs Windows 7. You attempt to migrate the user profiles and data from Computer1 to Computer2 by using User State Migration Tool (USMT) 4.0. During the migration, you receive the following error message:
“Gather was aborted because of an EFS file.”
You need to ensure that you can successfully migrate the user state from Computer1 to Computer2. What should you do?
A. Add the /efs:copyraw switch to the Loadstate command.
B. Add the /efs:copyraw switch to the Scanstate command.
C. Generate a new Encrypting File System (EFS) certificate on Computer2.
D. Export the Encrypting File System (EFS) certificate from Computer1 and import the certificate to Computer2.
Answer: B
Explanation:
You run ScanState on the source computer during the migration. You must run ScanState.exe on computers running Windows Vista and Windows 7 from an administrative command prompt. When running ScanState on a source computer that has Windows XP installed, you need to run it as a user that is a member of the local administrators group. The following command creates an encrypted store named Mystore on the file share named Migration on the file server named Fileserver that uses the encryption key Mykey: scanstate \\fileserver\migration\mystore /i:migapp.xml /i:miguser.xml /o /config:config.xml /encrypt /key:”mykey”Encrypted File OptionsYou can use the following options to migrate encrypted files. In all cases, by default, USMT 4.0 fails if an encrypted file is found unless you specify an /efs option. To migrate encrypted files, you must change the default behavior. EFS certificates will be migrated automatically when migrating to Windows Vista or Windows 7. Therefore, you should specify the /efs:copyraw option with the ScanState command to migrate the encrypted files
QUESTION 347
You have two computers named Computer1 and Computer2 that run Windows 7. Computer1 has two local user accounts named User1 and User2. On Computer1, you run Scanstate.exe /all \\server1\data\computer1. On Computer2, you run Loadstate.exe /lac:Pa$$w0rd \\server1\data\computer1. You need to ensure that User1 and User2 can log on to Computer2. What should you do on Computer2?
A. Enable all user accounts.
B. Modify the default password policy.
C. Modify the Allow log on locally user right.
D. Add User1 and User2 to the local Administrators group.
Answer: A
Explanation:
LoadState is run on the destination computer. You should install all applications that were on the source computer on the destination before you run LoadState. You must run Loadstate. exe on computers running Windows Vista and Windows 7 from an administrative command prompt. To load profile data from an encrypted store named Mystore that is stored on a share named Migration on a file server named Fileserver and which is encrypted with the encryption key Mykey, use this command: loadstate \\fileserver\migration\mystore /i:migapp.xml /i:miguser.xml /decrypt /key:”mykey” (local account create) /lac:[Password] Specifies that if a user account is a local (non- domain) account, and it does not exist on the destination computer, USMT will create the account on the destination computer but it will be disabled. To enable the account, you must also use the /lae option. If the /lac option is not specified, any local user accounts that do not already exist on the destination computer will not be migrated. Password is the password for the newly created account. An empty password is used by default.
QUESTION 348
You plan to capture a Windows 7 image by using the Windows Preinstallation Environment (Windows PE). You need to ensure that Windows PE supports the Windows Scripting Host (WSH). Which tool should you use?
A. Bcdedit.exe
B. Dism.exe
C. Imagex.exe
D. Oscdimg.exe
Answer: B
Explanation:
DismDeployment Image Servicing and Management (DISM) is a command-line tool used to service Windows images offline before deployment. You can use it to install, uninstall, configure, and update Windows features, packages, drivers, and international settings. Subsets of the DISM servicing commands are also available for servicing a running operating system. Windows 7 introduces the DISM command-line tool. You can use DISM to service a Windows image or to prepare a Windows PE image. DISM replaces Package Manager (Pkgmgr.exe), PEimg, and Intlcfg in Windows Vista, and includes new features to improve the experience for offline servicing. You can use DISM to perform the following actions:
– Prepare a Windows PE image.
– Enable or disable Windows features within an image.
– Upgrade a Windows image to a different edition.
– Add, remove, and enumerate packages.
– Add, remove, and enumerate drivers.
– Apply changes based on the offline servicing section of an unattended answer file.
– Configure international settings.
– Implement powerful logging features.
– Service operating systems such as Windows Vista with SP1 and Windows Server 2008.
– Service a 32-bit image from a 64-bit host and service a 64-bit image from a 32-bit host.
– Service all platforms (32-bit, 64-bit, and Itanium).
– Use existing Package Manager scripts.
DISM Command-Line Options To service a Windows image offline, you must apply or mount it. WIM images can be mounted using the WIM commands within DISM, or applied and then recaptured using ImageX. You can also use the WIM commands to list the indexes or verify the architecture for the image you are mounting. After you update the image, you must dismount it and then either commit or discard the changes you have made.NOT BcdeditBCDEdit is a command-line tool for managing BCD stores. It can be used for a variety of purposes, including creating new stores, modifying existing stores, adding boot menu options, and so on. BCDEdit serves essentially the same purpose as Bootcfg.exe on earlier versions of Windows, but with two major improvements: BCDEdit exposes a wider range of boot options than Bootcfg.exe, and BCDEdit has improved scripting support.NOT ImagexImageX is a command-line tool that enables original equipment manufacturers (OEMs) and corporations to capture, to modify, and to apply file- based disk images for rapid deployment. ImageX works with Windows image (.wim) files for copying to a network, or it can work with other technologies that use .wim images, such as Windows Setup, Windows Deployment Services (Windows DS), and the System Management Server (SMS) Operating System Feature Deployment Pack.NOT OscdimgOscdimg is a command-line tool for creating an image file (.iso) of a customized 32-bit or 64-bit version of Windows PE. You can then burn that .iso file to a CD-ROM or DVD-ROM. Oscdimg supports ISO 9660, Joliet, and Universal Disk Format (UDF) file systems.
QUESTION 349
You have a computer that runs Windows 7. You need to capture the operating system and all the computer configurations to a Windows image (WIM) file. What should you do before you capture the image?
A. Run Oscdimg.exe.
B. Run Windows System Image Manager (Windows SIM).
C. Open a command prompt that has elevated privileges.
D. Start the computer by using Windows Preinstallation Environment (Windows PE).
Answer: D
Explanation:
Windows PE To access a network share as an installation source from the client computer, you need to boot the client computer into the Windows Preintallation Environment (Windows PE) environment. The Windows PE environment is a minimally featured operating system that allows you to access diagnostic and maintenance tools as well as access network drives. Once you have successfully booted into the Windows PE environment, you can connect to the network share and begin the installation by running Setup.exe.NOT Windows SIMOpens Windows images, creates answer files, and manages distribution shares and configuration sets.NOT OscdimgOscdimg is a command-line tool for creating an image file (.iso) of a customized 32-bit or 64-bit version of Windows PE. You can then burn that .iso file to a CD-ROM or DVD-ROM. Oscdimg supports ISO 9660, Joliet, and Universal Disk Format (UDF) file systems.
QUESTION 350
You need to create a virtual hard disk (VHD) file that will be used to deploy Windows 7. The solution must minimize the performance impact caused by using a VHD. Which type of VHD should you create?
A. Differencing disk
B. Dynamically expanding disk
C. Fixed-size disk
D. Snapshot
Answer: C
Explanation:
Typically, you place the VHD on a second internal or external hard disk (although this is not essential). You then specify the VHD size and format settings. Microsoft recommends the default Fixed Size setting, but you can select Dynamic Expanding if you do not want to allocate the disk space. Fixed Size gives better performance and is more suitable in a production environment.

http://www.passleader.com/70-680.html
QUESTION 351
You are the network administrator for a large organization with many laptop users who go on the road. You want these users to be able to connect to the network without using a VPN or taking over the server console. What can you implement?
A. DirectAccess
B. Remote Access
C. Remote Desktop
D. Remote Server
Answer: A
Explanation:
DirectAccess enables remote users to work on their corporate network when they are away from the offi ce without the need of a VPN. As long as the remote user is connected to the Internet, DirectAccess will automatically connect the remote user to the corporate network without the need of any user intervention.
QUESTION 352
You are the network administrator for your organization. You have been asked by the owner of the company to verify that all drivers installed on the Windows 7 machines are signed drivers. How do you accomplish this task?
A. Run Verify.exe at the command prompt.
B. Run a scan in Device manager.
C. Run Sigverif.exe at the command prompt.
D. Run Drivers.exe at the command prompt.
Answer: C
Explanation:
Running the Sigverif.exe program will run a check against all the drivers installed on your machine and then notify you of any drivers that are unsigned.
QUESTION 353
You are the network administrator for your organization. You are asked by your manager to modify a few file extensions that are associated with Internet Explorer. How can you accomplish this task?
A. In Control Panel, open Default Programs and then click Set Associations. Set the proper file extensions.
B. In Internet Explorer, set extensions on the extension tab.
C. In Control Panel, open System and then click Set Associations. Set the proper file extensions.
D. In Internet Explorer, set extensions on the advanced tab.
Answer: A
Explanation:
The Default Programs icon in Control Panel allows you to set file extension associations to the various programs in Windows 7.
QUESTION 354
You are the network administrator for a large organization. You are in charge of implementing company policies. One company policy states that you have to prevent Internet Explorer from saving any data during a user’s browsing session. How do you accomplish this?
A. Set the Internet Security settings to disabled.
B. Run the browsers in the InPrivate session.
C. InPrivate sessions should be disabled.
D. Private sessions should be enabled.
Answer: B
Explanation:
The InPrivate session prevents the browsing history from being recorded and does not allow temporary internet files to be retained. Cookies, usernames, passwords, and form data will not remain in IE8 following the closing of the InPrivate session, nor will there be any footprints or data pertaining to the InPrivate browsing session.
QUESTION 355
You are the network administrator for a large organization. A user calls you and says that when they try to connect to the internal website, they are prompted for authentication. The user has the rights to access the internal site due to the fact that all users and computers are part of a domain and the internal website uses Integrated Windows Authentication. How do you make sure that the user is automatically authenticated when they connect?
A. Change the user ‘ s local permissions to administrator.
B. The Local site’s URL should be added to the Local internet zone.
C. The Local site’s security credentials should be added to the trusted sites zone.
D. The internet security level should be lowered to lowest.
Answer: B
Explanation:
Because all users and computers are part of the domain and the internal website uses Integrated Windows Authentication, once you add the URL to the Local internet zone properties, the Windows Authentication will take over.
QUESTION 356
You are the network administrator for your organization. Your organization has been using Windows XP, and you are now switching all users to Windows 7 Professional. Some of the XP applications do not run properly in Windows 7. How can you allow these applications to run on Windows 7?
A. Run the applications in XP mode.
B. Get newer versions of the applications.
C. Disable the Windows 7 Compatibility Mode.
D. Write your own shim to solve the issues.
Answer: A
Explanation:
Windows XP mode is available on Windows 7 Professional, Ultimate, and Enterprise editions and allows you to run XP applications on Windows 7 properly.
QUESTION 357
You are using Windows 7 Home edition and you have an XP application that worked well with XP but is having issues running on Windows 7. What steps can you take to help solve this issue?
A. Change the Applications security settings.
B. Change the Applications Compatibility Mode to Windows XP.
C. Enable the Windows 7 operating system to XP Compatible.
D. Upgrade the application.
Answer: B
Explanation:
If a Windows XP application worked before but it is not working correctly in Windows 7, you can set that application to run in Compatibility Mode for a previous operating system.
QUESTION 358
Which versions of Windows 7 has XP mode automatically built into the operating system? Choose all that apply.
A. Install and use Windows Virtual PC
B. Enterprise Edition
C. Ultimate Edition
D. Professional Edition
Answer: A
Explanation:
Windows Virtual PC allows you to install previous versions of 32-bit operating system like XP so that you can continue to run applications.
QUESTION 359
You are the network administrator for a large organization. One of your users calls you and states that they think they are having issues with their network card. What tool can you use to see if the hardware is working properly?
A. Device Hardware Utility
B. Manage Hardware Utility
C. Device Manager
D. Device Configuration
Answer: C
Explanation:
Device Manager is the utility included with Windows 7 that allows you to configure and manage your devices and hardware. You can also confi gure your drivers within Device Manager.
QUESTION 360
You are the network administrator for a large organization. You have a Windows 7 machine that is working fine but you downloaded a newer version of the network adapter driver. You install the new network adapter driver on the Windows 7 machine. After you load the driver, the network device stops working properly. Which tool should you use to help you fix the problem?
A. Driver Rollback
B. Driver Repair Utility
C. Reverse Driver Application
D. Windows 7 Driver Compatibility tool
Answer: A
Explanation:
Driver Rollback allows you to replace a newly installed driver with the previous driver. You can do the driver rollback using the Device Manager utility.

http://www.passleader.com/70-680.html