Free Download 100% Pass Ensure 299q 70-689 New Exam Dumps! The new 70-689 vce dumps from PassLeader cover all new exam questions, which will ensure your 70-689 exam 100% pass! Now the free new version VCE Player along with the VCE braindumps, and the 70-689 PDF dumps are all available now!
keywords: 70-689 exam,299q 70-689 exam dumps,299q 70-689 exam questions,70-689 pdf dumps,70-689 vce dumps,70-689 braindumps,70-689 practice test,Microsoft Upgrading Your Skills to MCSA Windows 8

QUESTION 191
You administer a company network that includes computers that run Windows 8 Enterprise in an Active Directory domain. The company has purchased a subscription to Windows Intune. Corporate security policy requires that computers in the accounting department have file and program activity logged. A user in the accounting department uses a computer that is managed by Windows Intune. You need to ensure that file and program activity is always monitored on this computer. What should you do?
A. Create a new Windows Firewall Setting policy in the Windows Intune Admin Console.
B. In the Windows Intune Admin Console, create a new Windows Intune Agent Settings policy that uses the recommended settings.
C. Create a new Windows Intune Mobile Security policy in the Windows Intune Admin Console.
D. Create and deploy a custom policy in the Windows Intune Center Settings template.
Answer: B
QUESTION 192
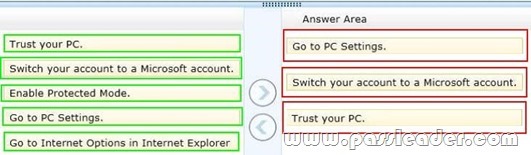
Drag and Drop Questions
You use a desktop computer and a laptop, both of which run Windows 8. You use a Microsoft account to log on to the desktop computer and a local user account to log on to the laptop. The desktop computer is joined to the HomeGroup and the laptop is a member of a workgroup. When you access a frequently visited website from your laptop, Internet Explorer saves your password. When you visit the website from your desktop computer, you are prompted to enter your password. You need to sync your saved password from your laptop to your desktop computer. Which three actions should you perform on the laptop in sequence? (To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.)
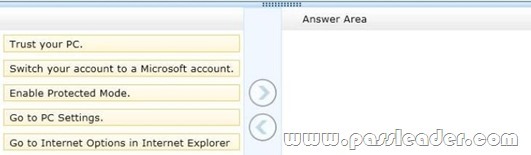
Answer:
QUESTION 193
Drag and Drop Questions
You support computers that run Windows 8 Pro. Your company recently purchased 200 new desktop computers. Company policy requires that the desktop computers include a recovery partition. The partition must contain a bootable image that includes support for incoming Remote Desktop connections. You need to configure the desktop computers to comply with company policy. Which four actions should you perform in sequence? (To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.)
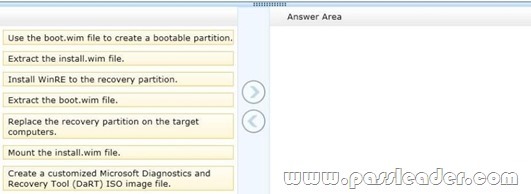
Answer:
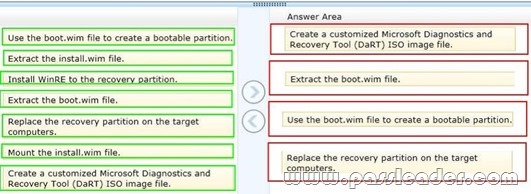
Explanation:
After you have finished running the Microsoft Diagnostics and Recovery Toolset (DaRT) 8.0 Recovery Image wizard and created the recovery image, you can extract the boot.wim file from the ISO image file and deploy it as a recovery partition in a Windows 8 image. A partition is recommended, because any corruption issues that prevent the Windows operating system from starting would also prevent the recovery image from starting.
Reference: How to Deploy the DaRT Recovery Image as Part of a Recovery Partition.
QUESTION 194
You have computers that run Windows 8 Enterprise. Microsoft BitLocker Administration and Monitoring (MBAM) is deployed on your network on a server named MBAM1. Company policy requires that within 2 hours of being started, computers that have the MBAM client installed prompt users to enable BitLocker. You need to make changes to the Configure MBAM Services Group Policy settings. Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.)
A. Set MBAM Recovery and Hardware service endpoint to MBAM1.
B. Set Enter status reporting frequency (in minutes) to 120.
C. Set MBAM Status reporting endpoint to MBAM1.
D. Set Select Bitlocker Recovery Information to store to Recovery password and key package.
E. Set Select Bitlocker Recovery Information to store to Recovery password only.
F. Set Enter client checking status frequency (in minutes) to 120.
Answer: AC
QUESTION 195
You administer computers that run Windows 8 Enterprise in an Active Directory domain. Your company has purchased a subscription to Windows Intune. Users access a Microsoft Exchange environment by using the Mail tile. The Microsoft Exchange environment is connected to Windows Intune. Company security policy defines the minimum length of passwords and required encryption settings. You need to create a Windows Intune policy that meets the security policy requirements. What should you do?
A. Create a new Windows Intune Center Settings policy.
B. Create a new Windows Intune Agent Settings policy.
C. Create a new Windows Intune Mobile Security policy.
D. Create a new Windows Firewall Settings policy.
Answer: C
QUESTION 196
You support computers that run Windows 8 Enterprise. Your company has started testing Application Virtualization (App-V) applications on several laptops. You discover that the App-V applications are available to users even when the laptops are offline. You need to ensure that the App-V applications are available to users only when they are connected to the company network. What should you do?
A. Configure mandatory profiles for laptop users.
B. Reset the App-V client FileSystem cache.
C. Disable the Disconnected operation mode.
D. Change user permissions to the App-V applications.
Answer: C
QUESTION 197
At work, you use a desktop computer that runs Windows 8 Pro. At home, you use a laptop that runs Windows 8. You use the same Microsoft account to log on to both computers. You want to use the same settings for both computers. You need to ensure that all computer settings, including stored passwords, are synced between the computers. What should you do?
A. Add both computers to the same Active Directory domain.
B. Use the same local accounts for both computers.
C. Install SkyDrive for Windows on both computers.
D. Designate both computers as trusted PCs.
Answer: D
QUESTION 198
Your company recently purchased 10 new desktop computers for a remote unconnected location. All of the desktop computers have the same hardware configuration. You install Windows 8 Pro on a reference computer and install a custom driver to support the video adapter. You want to create an image of the reference desktop that retains the custom driver in the image. You need to edit the unattended answer file. Which setting in the unattended answer file should you edit?
A. Microsoft-Windows-PnPSysprep | PersistAllDeviceInstalls
B. Microsoft-Windows-PnPSysprep | DoNotCleanUpNonPresentDevices
C. Microsoft-Windows-PnpCustomizattonNonWinPE | DriverPaths
D. Microsoft-Windows-Shell-Setup | OEMInformation
Answer: A
QUESTION 199
Drag and Drop Questions
You administer 50 laptops that run Windows 7 Professional 32-bit. You want to install Windows 8 Pro 64-bit on every laptop. Users will keep their own laptops. You need to ensure that user application settings, Windows settings, and user files are maintained after Windows 8 Pro is installed. Which four actions should you perform in sequence? (To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.)
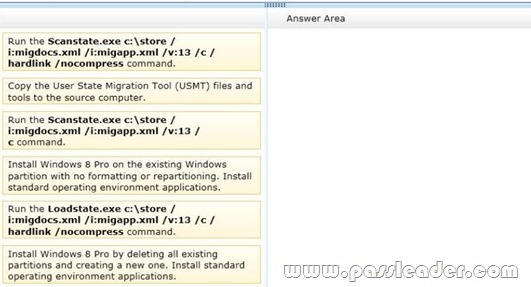
Answer:
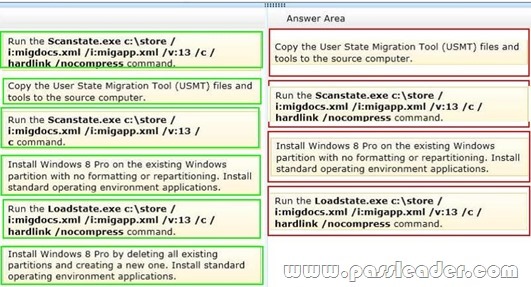
Explanation:
* You use the User State Migration Tool (USMT) 5.0 when hardware and/or operating system upgrades are planned for a large number of computers. USMT manages the migration of an end- user’s digital identity by capturing the user’s operating-system settings, application settings, and personal files from a source computer and reinstalling them on a destination computer after the upgrade has occurred. One common scenario when only the operating system, and not the hardware, is being upgraded is referred to as PC refresh. A second common scenario is known as PC replacement, where one piece of hardware is being replaced, typically by newer hardware and a newer operating system.
* Scenario: PC-refresh using a hard-link migration store A company has just received funds to update the operating system on all of its computers to Windows 8. Each employee will keep the same computer, but the operating system on each computer will be updated. In this scenario, an administrator uses a hard-link migration store to save each user state to their respective computer. The administrator runs the ScanState command-line tool on each computer, specifying the /hardlink /nocompress command-line options. ScanState saves the user state to a hard-link migration store on each computer, improving performance by minimizing network traffic as well as minimizing migration failures on computers with very limited space available on the hard drive. On each computer, the administrator installs the company’s SOE which includes Windows 8 and other company applications. The administrator runs the LoadState command-line tool on each computer. LoadState restores each user state back on each computer.
Reference: User State Migration Toolkit (USMT) Reference.
QUESTION 200
You are a systems administrator for your company. The company has employees who work remotely by using a virtual private network (VPN) connection from their computers, which run Windows 8 Pro. These employees use an application to access the company intranet database servers. The company recently decided to distribute the latest version of the application through using a public cloud. Some users report that every time they try to download the application by using Internet Explorer, they receive a warning message that indicates the application could harm their computer. You need to recommend a solution that prevents this warning message from appearing, without compromising the security protection of the computers. What should you do?
A. Publish the application through a public file transfer protocol (FTP) site.
B. Publish the application through an intranet web site.
C. Instruct employees to disable the SmartScreen Filter from within the Internet Explorer settings.
D. Publish the application to Windows Store.
Answer: B

70-689 exam dumps, 70-689 exam questions, 70-689 vce dumps, 70-689 pdf dumps, 70-689 practice test, 70-689 study guide: http://www.passleader.com/70-689.html
QUESTION 201
You support desktop computers that run Windows 8 Pro and are used as guest terminals in a reception area. They are connected to the Internet and are configured with automatic logon by using a local user account. You discover new applications on the Start screen of the computers. You need to restrict access to Windows Store for local user accounts on the computers. What should you do?
A. From Local Computer Policy, navigate to App Package Deployment and disable All Trusted Apps to Install.
B. From Local Computer Policy, select Store and enable Turn off the Store application.
C. From Local Computer Policy, select Store and disable Turn off Automatic Downloads for Updates.
D. From Local Computer Policy, select Store and disable Allow Store to install apps on Windows To Go workspaces.
Answer: B
QUESTION 202
You support laptops that run Windows 8 Pro and are members of an Active Directory domain. The domain is configured with user folder redirection by using a Group Policy Object (GPO). Loopback group policies are not used. Your company has decided to deploy tablets to all managers, for use as secondary computers. Tablets will be added to the domain. You need to ensure that the folder redirection settings are applied only to laptops. What should you do?
A. Apply one GPO to the managers’ laptops and another GPO to the tablets.
B. Assign the msDS-Primary Computer attribute for the managers’ user domain accounts.
C. Assign the msDS-Primary Computer attribute for the computer domain accounts on the managers’ laptops.
D. Block the managers’ tablets from receiving the GPO.
Answer: B
QUESTION 203
You administer desktop computers on your company network. You want to deploy a WIM file of Windows 8 Enterprise to 15 desktop computers that have a third-party iSCSI adapter installed. The hardware vendor provided a device driver to support this adapter. You need to update the image to ensure that the device driver is installed when you deploy the image. What should you do?
A. Run the dism.exe tool and specify the fadd-driver parameter.
B. Download and run the drvload.exe tool and specify the path to the driver .inf file.
C. Download and run the imagex.exe tool and specify the /remount parameter.
D. Run the dism.exe tool and specify the /append-image parameter.
Answer: A
QUESTION 204
You have a client computer named Computer1 that runs Windows 8 Enterprise. Computer1 has a Trusted Platform Module (TPM) chip installed and the operating system volume is encrypted by using BitLocker Drive Encryption (BitLocker). You plan to upgrade the BIOS of Computer1. You need to recommend a solution that meets the following requirements:
– Ensures that the drive remains encrypted
– Avoids the need to perform a BitLocker recovery
– Ensures that Windows can start after the BIOS is upgraded
– Minimizes the time required to complete the BIOS upgrade
What should you include in the recommendation?
A. From the command prompt, run manage-bde and specify the -protectors parameter and the – disable parameter.
B. From the command prompt, run manage-bde and specify the -protectors parameter and the – delete parameter.
C. From the Trusted Platform Module (TPM) Management console, click Turn TPM Off from the Actions menu.
D. From the command prompt, run tpmvscmgr.exe and specify the destroy parameter.
Answer: A
Explanation:
* For mass BIOS updates, create a script that disables BitLocker, installs the update, reboots the system and then re-enables BitLocker.
* manage-bde -autounlock {-enable | -disable | -ClearAllKeys} Volume [-ComputerName Name] -disable
Disables automatic unlocking for a data drive.
* The Disable-BitLocker cmdlet disables BitLocker Drive Encryption for a BitLocker volume. When you run this cmdlet, it removes all key protectors and begins decrypting the content of the volume.
QUESTION 205
At work, you use a desktop computer that runs Windows 8 Pro. At home, you use a laptop that runs Windows 8. You use the same Microsoft account to log on to both computers. You want to use the same settings for both computers. You need to ensure that all computer settings, including stored passwords, are synced between the computers. What should you do?
A. Enable the Guest account on both computers.
B. Designate both computers as trusted PCs.
C. Add both computers to the same workgroup.
D. Join both computers to the same HomeGroup
Answer: B
QUESTION 206
You are a Windows 8 user. Your organization has purchased an Office 365 subscription. You install Microsoft Lync and Microsoft Outlook on your computer. You need to connect Office 365 to Lync and Outlook. What should you do?
A. Run the Office Professional Plus setup from the Office 365 portal.
B. Run the Windows Mail application. Add a new account by using your Office 365 credentials.
C. Run the People application. Add a new account by using your Office 365 credentials.
D. Run the Office 365 desktop setup from the Office 365 portal.
Answer: D
QUESTION 207
You administer desktop computers on your company network. You want to deploy a WIM file of Windows 8 Enterprise to 15 desktop computers that have a third-party iSCSI adapter installed. The hardware vendor provided a device driver to support this adapter. You need to update the image to ensure that the device driver is installed when you deploy the image. What should you do?
A. Download and run the imagex.exe tool and specify the /remount parameter.
B. Run the dism.exe tool and specify the /append-image parameter.
C. Download and run the drvload.exe tool and specify the path to the driver .inf file.
D. Run the dism.exe tool and specify the /add-driver parameter.
Answer: D
Explanation:
Driver Servicing Command-Line Options
Reference: http://technet.microsoft.com/en-us/library/dd799258(v=ws.10).aspx
The driver servicing commands can be used on an offline image to add and remove drivers based on the INF file, and on a running operating system (online) toenumerate drivers.
QUESTION 208
Drag and Drop Questions
You support computers that run Windows 8 Pro. Your company recently purchased 200 new desktop computers. Company policy requires that the desktop computers include a recovery partition. The partition must contain a bootable image that includes support for incoming Remote Desktop connections. You need to configure the desktop computers to comply with company policy. Which four actions should you perform in sequence? (To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.)
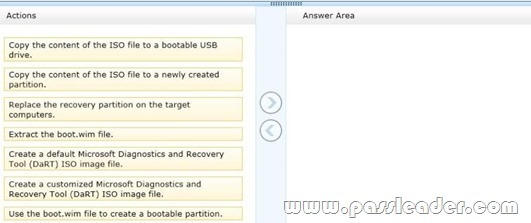
Answer:
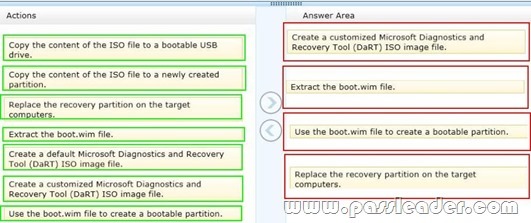
Explanation:
Note:
After you have finished running the Microsoft Diagnostics and Recovery Toolset (DaRT) 8.0 Recovery Image wizard and created the recovery image, you can extract the boot.wim file from the ISO image file and deploy it as a recovery partition in a Windows 8 image. A partition is recommended, because any corruption issues that prevent the Windows operating system from starting would also prevent the recovery image from starting. Reference: How to Deploy the DaRT Recovery Image as Part of a Recovery Partition
QUESTION 209
Your network contains an Active Directory domain and a subscription to Microsoft Office 365. Users discover that they must change their Active Directory password more frequently than their Office 365 password. You need to ensure that the password policies for Office 365 and for Active Directory are the same. What should you do?
A. From the Office 365 portal, under Subscriptions, click Manage.
B. From the Windows Azure Active Directory Module for Windows PowerShell, run Set- MsolUserPassword.
C. From the Office 365 portal, under Management, click Users.
D. From the Office 365 portal, under Management, click Domains.
Answer: C
Explanation:
In the Office 365 portal, click Admin > Users (under Management in the navigation pane). On the Users page, select a user, and then click Edit.
Note:
* Some of the options can be managed by using the Office365 Web interface and some task only by using PowerShell.
* Office 365 users Password management verses the “Standard” Domain Active directory is a little bit restricted. For example: configure password policy parameters such as – Enforce password history, Minimum password length, Password must meet complexity requirements cannot be configured by the office 365 administrator. At the current time, the options that related to Office 365 users Password management are: reset the user password and setting the number of maximum number of days or password expiration (the default is 90 days).
QUESTION 210
You administer computers that run Windows 8 Enterprise in an Active Directory domain in a single Active Directory Site. All user account objects in Active Directory have the Manager attribute populated. The company has purchased a subscription to Windows Intune. The domain security groups are synchronized with the Microsoft Online directory. You create a Windows Intune group that specifies a manager as a membership criterion. You notice that the group has no members. You need to ensure that users that meet the membership criteria are added to the Windows Intune group. What should you do?
A. Force Active Directory replication within the domain.
B. Ensure that all user accounts are identified as synchronized users.
C. Ensure that the user who is performing the search has been synchronized with the Microsoft Online directory.
D. Synchronize the Active Directory Domain Service (AD DS) with the Microsoft Online directory.
Answer: B

http://www.passleader.com/70-689.html