PassLeader supply the newest 196q 70-685 vce dumps and 70-685 pdf dumps, the latest 196q 70-685 braindumps are the best dumps with all new 70-685 exam questions, it will let you passing 70-685 exam easily and quickly. Now going to passleader.com and download the valid 70-685 exam dumps and FREE VCE PLAYER!
keywords: 70-685 exam,196q 70-685 exam dumps,196q 70-685 exam questions,70-685 pdf dumps,70-685 vce dumps,70-685 braindumps,70-685 practice test,70-685 study guide,Pro: Windows 7, Enterprise Desktop Support Technician Exam

QUESTION 31
All client computers on your company network run Windows 7 and are members of an Active Directory Domain Services domain. Your company policy requires that all unnecessary services be disabled on the computers. The Sales department staff has been provided with new mobile broadband adapters that use the Global System for Mobile Communications (GSM) technology. You need to ensure that portable computers can connect to the broadband GSM network. Which service should be enabled on the portable computers?
A. WLAN AutoConfig
B. WWAN AutoConfig
C. Computer Browser
D. Portable Device Enumerator Service
Answer: B
QUESTION 32
All client computers on your company network run Windows 7 and are members of an Active Directory Domain Services domain. Employees using portable computers report that they get connected to a coffee shop wireless network from the company conference room. You need to ensure that the employees connect to the company wireless network by default from anywhere within the company premises. What should you do?
A. Configure the Network authentication (Shared mode) setting.
B. Apply a Wireless Network Policy to set the network type to WPA-PSK.
C. Apply a Wireless Network Policy to automatically connect to the company wireless network.
D. Apply a Wireless Network Policy to set the company wireless network as the preferred network.
Answer: D
QUESTION 33
All client computers on your company network run Windows 7 and are members of an Active Directory Domain Services domain. All portable computers connect only to the 802.1X-authenticated wireless network. Wireless settings are set through the domain’s Group Policy. You discover that new portable computers cannot be joined to the domain. You need to ensure that new portable computers can be joined to the domain. What should you do?
A. Connect the portable computers to the wireless network by using a Bootstrap Profile.
B. Connect the portable computers to the wireless network by using a Non-Broadcast Profile.
C. Connect the portable computers to the domain by using smart card authentication.
D. Connect the portable computers to the domain by using network security key authentication.
Answer: A
QUESTION 34
Your network contains a wired network and a wireless network. Users report that they experience intermittent problems accessing network resources when they connect to the internal wireless network. You discover that an unsecured rogue wireless access point uses the same Service Set Identifier (SSID) as the internal wireless network. You need to ensure that the users only connect to the internal wireless network. What should you do?
A. Configure a Windows Connect Now Group Policy.
B. Configure a Wireless Network (IEEE 802.11) Policy.
C. Delete the rogue network from the Network and Sharing Center on each computer.
D. Create a Connection Manager Administration Kit (CMAK) profile and deploy it to all users.
Answer: B
QUESTION 35
All client computers on your company network run Windows 7 and are members of an Active Directory Domain Services domain. All servers run Windows Server 2008 R2 and are located in the main office. A remote office connects to the main office by using a cellular network. Employees at the remote office frequently download a daily report from an IIS Web server at the main office, which causes them to incur excessive pay per bandwidth usage costs. You need to decrease the network bandwidth usage costs incurred by the remote office. What should you do?
A. Implement DirectAccess.
B. Implement VPN with compression.
C. Implement Distributed File System.
D. Configure Branch Cache.
Answer: D
QUESTION 36
Your company uses portable computers that run Windows 7. The Sales department staff use Wireless Wide Area Network (WWAN), WLAN, and wired network connections to work from a remote location. The Sales department staff reestablish their secure connections and restart applications frequently. You need to ensure that the employees are able to work without unnecessary interruptions. What should you do?
A. Create a Group Policy to configure preferred wireless access points
B. Configure Group Policy preferences to create multiple VPN connections
C. Configure each portable computer to use the VPN Reconnect feature
D. Configure each portable computer to use the Extensible Authentication Protocol
Answer: C
QUESTION 37
Your company has a main office and two branch office locations. All client computers on your company network run Windows 7 and are members of an Active Directory Domain Services domain. All servers run Windows Server 2008 R2 and are located in the main office. Branch office employees use a slow WAN link with high latency to access files on a network share located in the main office. You need to meet the following requirements:
– Reduce WAN link utilization
– Improve user response time when accessing files
What should you do?
A. Configure BranchCache in Hosted Mode.
B. Configure BranchCache in Distributed Mode.
C. Configure the Default Cache Size setting by using Group Policy.
D. Configure the Configure Slow link speed setting by using Group Policy.
Answer: B
QUESTION 38
All client computers on your company network run Windows XP and are members of an Active Directory Domain Services domain. You plan to migrate all computers to Windows 7. You also plan to deploy a new VPN server to support remote network access for the computers. You need to ensure that all computers will be supported for remote access during the migration to Windows 7. What should you do?
A. Set the VPN server to Layer 2 Tunneling Protocol.
B. Set the VPN server to Secure Socket Tunneling Protocol.
C. Set the VPN server to Internet Key Exchange version 2.
D. Configure the Direct Access feature on the VPN server.
Answer: A
QUESTION 39
All client computers on your company network run Windows 7. All servers in your company run Windows Server 2008 R2. Employees use a VPN connection to connect to the company network from a remote location. Software updates are not being applied to the client computers because employees log off before the updates are applied. You need to ensure that software updates are always applied to the client computers. What should you do?
A. Configure the Direct Access feature.
B. Configure the VPN Reconnect feature.
C. Use Group Policy to publish a package that contains the software updates.
D. Use Group Policy to redeploy a package that contains the software updates.
Answer: A
QUESTION 40
All client computers on your company network run Windows 7. All servers in your company run Windows Server 2008 R2. Employees use a VPN connection to connect to the company network from a remote location. Employees remain connected to the VPN server to browse the Internet for personal use. You need to ensure that employees are unable to use the VPN connection for personal use. What should you do?
A. Configure the VPN connection to append a connection-specific DNS suffix.
B. Configure the VPN connection to use machine certificates for authentication.
C. Use Group Policy to disable the Use default gateway on remote network setting on each client computer.
D. Use Group Policy to configure the firewall on each computer to block outgoing connections when using the VPN connection.
Answer: C

http://www.passleader.com/70-685.html
QUESTION 41
All client computers on your company network run Windows 7. Employees use Windows Internet Explorer 8 to access Web sites. You discover that some computers are infected with malicious software. Employees are able to access Web sites that might have been compromised by malicious software. You need to configure the settings in Internet Explorer 8 to prevent malicious software from being installed on the computers. What should you do?
A. Configure Popup Blocker.
B. Configure SmartScreen Filter.
C. Add the sites to the Local intranet zone.
D. Add company-approved Web sites to the Compatibility View List.
Answer: B
QUESTION 42
All client computers on your company network run Windows 7 and are members of a Windows Server 2008 R2 domain. The R&D department staff are local administrators on their computers and are members of the R&D global security group. A new version of a business software application is available on the network. You plan to apply an AppLocker security policy to the R&D group. You need to ensure that members of the R&D group are not allowed to upgrade the software. What should you do?
A. Create an Audit only restriction based on the version of the software.
B. Create an Audit only restriction based on the publisher of the software.
C. Create an Enforce rule restriction based on the version of the software.
D. Create an Enforce rule restriction based on the publisher of the software.
Answer: C
Explanation:
http://technet.microsoft.com/en-us/library/ee619725(WS.10).aspx http://sourcedaddy.com/windows-7/applocker-rule-types.html
QUESTION 43
A company has computers running Windows 7 Enterprise and has hardware capable of displaying Windows Aero. A user is unable to use Windows Flip 3D and does not see previews of open windows from the taskbar. You need to ensure that the computer displays Aero. What should you do? (Choose all that apply.)
A. Upgrade to Windows 7 Ultimate.
B. Update to the latest video driver.
C. Run the Aero troubleshooter tool.
D. Add additional RAM in the computer.
E. Change the theme to an Aero theme.
F. Re-run the assessment for the Windows Experience Index.
Answer: BCE
QUESTION 44
Your company has a main office and a branch office. The network contains a single Active Directory domain. All computers are members of the domain. Five users in the branch office report that their Windows 7 computer is slow when it runs multiple applications. From your computer, you need to identify the application that uses the most processor on the computers. Which tool should you use?
A. Performance Monitor
B. Reliability Monitor
C. Resource Monitor
D. System Information
Answer: A
Case Study 1 – Consolidated Messenger (QUESTION 45 – QUESTION 49)
Scenario
You are an enterprise desktop support technician for Consolidated Messenger.
Network Configuration
The company has three offices named Office1, Office2, and Office3. The offices connect to each other over the Internet by using VPN connections. Each office has an 802.11g wireless access point. All wireless access points are configured to use Radius01 for authentication.
Active Directory Configuration
The network contains one Active Directory domain named consolidatedmessenger.com. The relevant organizational unit structure is shown in the following diagram:

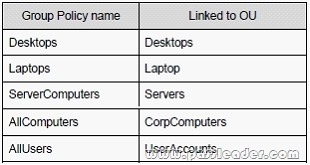
The relevant Group Policy objects (GPOs) in the domain are configured as shown in the following table:
Applications
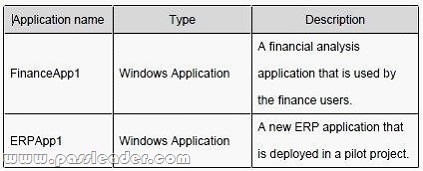
The relevant applications on the network are shown in the following table:
Server Configuration
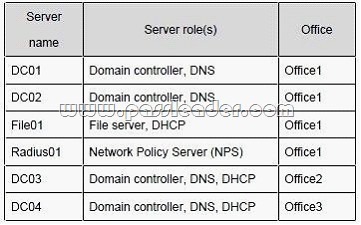
The relevant servers are configured as shown in the following table:
Client Configuration
Each office has 500 desktop computers that run Windows 7 Enterprise. There are 250 mobile users that travel regularly between all three offices. The mobile users have laptop computers that run Windows 7 Enterprise. To prevent the spread of malware, the company restricts the use of USB devices and only allows the use of approved USB storage devices.
Printers
The marketing group has several printers that are shared on File01. A shared printer name Printer1 is a high-performance, black-and-white printer. A shared printer named Printer2 is a high-definition, photo-quality, color printer. Printer2 should only be used to print marketing brochures.
QUESTION 45
The chief financial officer (CFO) releases new guidelines that specify that only users from Finance are allowed to run FinanceApp1. Users in the Marketing OU report that they can run FinanceApp1. You need to ensure that only users in the Finance OU can run FinanceApp1. What should you do?
A. In the AllComputers GPO, create a new AppLocker executable rule.
B. In the Desktops GPO and the Laptops GPO, create a new Windows Installer rule.
C. In the AllComputers GPO, create a software restriction policy and define a new hash rule.
D. In the Desktops GPO and the Laptops GPO, create a software restriction policy and define a new path rule.
Answer: A
Explanation:
You might want to deploy application control policies onto Windows operating systems earlier than Windows Server 2008 R2 or Windows 7. You can use AppLocker policies only on the supported editions of Windows Server 2008 R2 and Windows 7, but you can use SRP on supported editions of Windows beginning with Windows Server 2003 and Windows XP.
http://technet.microsoft.com/en-us/library/ee460955(WS.10).aspx
http://technet.microsoft.com/en-us/library/dd548340(WS.10).aspx
QUESTION 46
The help desk reports that users in the Marketing OU print draft documents, e-mails, and other miscellaneous documents on Printer2. You need to recommend a solution so that marketing users print documents to Printer1 by default. What should you do?
A. Enable printer pooling.
B. Configure Group Policy Preferences.
C. Modify the priorities of the shared printers.
D. Modify the permissions of the shared printers.
Answer: B
Explanation:
http://technet.microsoft.com/en-us/library/cc732092.aspx
Action: This type of preference item provides a choice of four actions: Create, Replace, Update, and Delete.
The behavior of the preference item varies with the action selected and whether the printer connection already exists.
Set this printer as the default printer – Select this check box to make the shared printer connection the default Windows printer for the current user. Only if a local printer is not present – Select this check box to bypass changing the default printer if there is a local printer configured on the computer. This setting is unavailable until you select the Set this printer as the default printer check box.
Note: A local printer is any printer that is not connected to a shared network printer. This includes physical printers connected to parallel, serial, and USB ports, TCP/IP printers, and virtual printers installed through software.
To create a new Shared Printer preference item
Open the Group Policy Management Console. Right-click the Group Policy object (GPO) that should contain the new preference item, and then click Edit. In the console tree under User Configuration, expand the Preferences folder, and then expand the Control Panel Settings folder.
Right-click the Printers node, point to New, and select Shared Printer. In the New Shared Printer Properties dialog box, select an Action for Group Policy to perform. Enter shared printer settings for Group Policy to configure or remove. Click the Common tab, configure any options, and then type your comments in the Description box.
Click OK. The new preference item appears in the details pane.
QUESTION 47
Users in the ERPApp1 pilot project report intermittent application issues. You need to consolidate all application events for the users in a central location. What should you do?
A. Configure event subscriptions.
B. Configure the Advanced Audit Policy Configuration settings.
C. Create a custom view in Event Viewer.
D. Create a user-defined Data Collector Set.
Answer: A
Explanation:
http://www.youtube.com/watch?v=4xxKPgT5irU
http://www.youtube.com/watch?v=fKelHBve57k
QUESTION 48
The Office1 network link is brought offline for emergency maintenance. Users in Office2 and Office3 report that they cannot connect to the wireless network. You need to recommend changes to ensure that users in all offices can connect to the wireless network if a WAN link fails. What should you recommend?
A. that redundant DHCP scopes be created
B. that additional RADIUS servers be deployed
C. that universal group caching be implemented
D. that additional default gateways be configured
Answer: B
QUESTION 49
The company purchases 500 USB flash drives from a new hardware vendor and distributes them to the users. The help desk reports that the users are unable to access the new USB flash drives. You need to ensure that users can save data on the USB flash drives. What should you do?
A. Instruct the help desk to modify the BitLocker settings.
B. Instruct the help desk to modify the Windows Defender settings.
C. Request that an administrator modify the driver signing policy.
D. Request that an administrator modify the device installation restriction policy.
Answer: D
Case Study 2 – City Power & Light (QUESTION 50 – QUESTION 54)
Scenario
You are an enterprise desktop support technician for City Power & Light. City Power & Light is a utility company. The company has a main office and a branch office. The main office is located in Toronto. The branch office is located in Boston. The main office has 1,000 employees. The branch office has 10 employees.
Active Directory Configuration
The network contains a single Active Directory domain named cpandl.com. The functional level of the forest is Windows Server 2008 R2.
Server Configuration
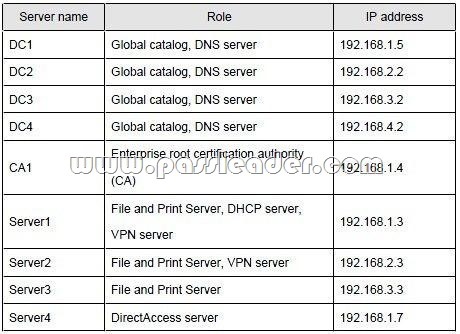
All servers run Windows Server 2008 R2. The relevant servers in the main office are configured as shown in the following table:
All computers in the main office are configured to use DHCP. All computers in the branch office are configured to use static IP addresses.
User Information
– All user accounts are standard user accounts.
– All client computers run Windows 7 Enterprise.
– Each portable computer has a PPT P-based VPN connection to the internal network.
Corporate Security Guidelines
– All users must be granted the least privileges possible.
– All locally stored documents must be encrypted by using Encrypting File System (EFS).
– The hard disk drives on all port able computers must be encrypted by using Windows BitLocker Drive Encryption (BitLocker).
– All encryption certificates must be stored on smart cards.
The company is deploying a new application. When users attempt to install the application, they receive an error message indicating that they need administrative privileges to install it.
QUESTION 50
You need to recommend a solution to ensure that users can install the application. The solution must adhere to the corporate security guidelines. What should you recommend?
A. Publish the application by using a Group Policy.
B. Disable User Account Control (UAC) by using a Group Policy.
C. Add all domain users to the local Power Users group by using Restricted Groups.
D. Add the current users to the local Administrators group by using Group Policy preferences.
Answer: A
Explanation:
http://magalan.co.uk/install_software_via_group_policy.html

http://www.passleader.com/70-685.html